Stay one step ahead.
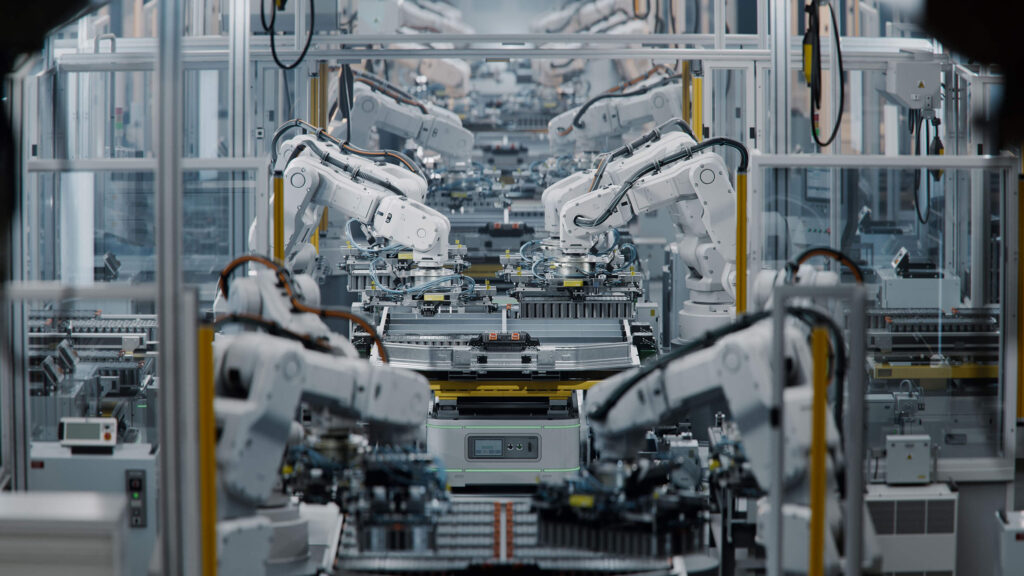
Secure your operations with IRON OT.
IRON OT specialises in industrial cybersecurity, helping organisations effectively protect their operations against modern cyber threats.
We design, implement, and manage Cybersecurity Management Systems for Operational Technology (OT) in line with ISA/IEC 62443, as well as Information Security Management Systems for IT in accordance with ISO/IEC 27001, ensuring seamless alignment between the two. All solutions are delivered in full compliance with the latest EU NIS2 legislation.